We have already reported about the Windows swap file in the past. We showed you how you can change the size of the Windows swap file or how it is automatically deleted when Windows shuts down .
Today we would like to show you how you can encrypt the Windows swap file . As a rule, the content of the swap file is stored unencrypted on the data carrier, the HDD or SSD and is therefore easily accessible to any attacker. However, since contents of the main memory (RAM) are swapped out in the Windows swap file, sensitive information can also be among the stored information, which is then stored unencrypted on the data carrier .
For this reason, Microsoft has created the option to encrypt the Windows swap file and thus increase system security.
Encrypt paging file by changing the registry
In order to encrypt the swap file (pagefile.sys) you must first open the Windows registry editor “regedit.exe” and open the following registry branch.
Computer HKEY_LOCAL_MACHINE SYSTEM CurrentControlSet Policies
A new DWORD 32-bit value with the following name must be created here.
NtfsEncryptPagingFile
We have shown this to you below.
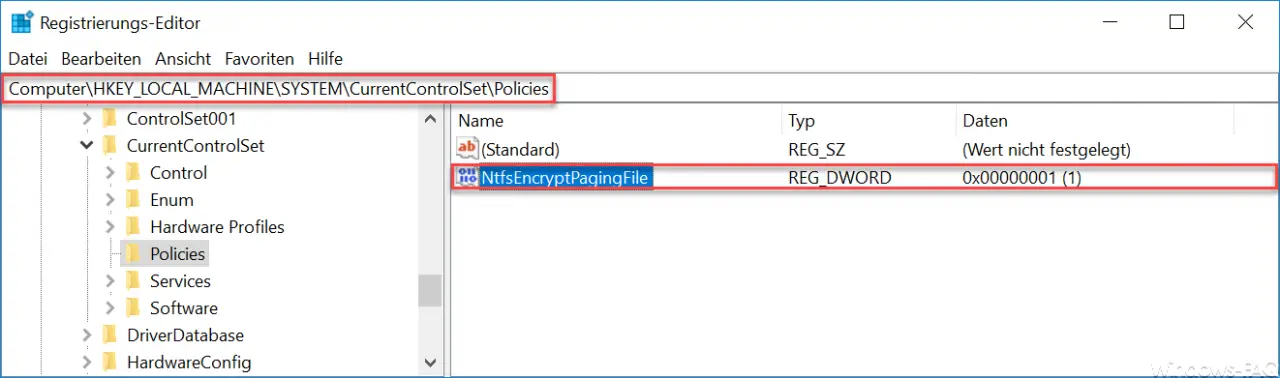
You should definitely note that this value ” NtfsEncryptPagingFile ” is also created as a DWORD 32 value for Windows 64-bit systems . Otherwise the encryption of Pagefile.sys will not work.
After you have created the new value, you must assign it the value “1” .
A Windows restart is then due and Windows will now encrypt all data that is moved to the swap file.
You can find more information about the Windows swap file in these articles:
– Deactivate Windows swap file
– Delete Pagefile.sys (Windows swap file) when shutting down Windows via registry change